One new organization becomes a ransomware victim every 10 seconds, and one in five Americans have now been the victim of a ransomware attack.
Is your organization prepared for an attack with a cybersecurity plan that covers everything from prevention to incident response plans? If not, what downtime costs can you expect?
Do You Really Need a Cybersecurity Plan?
Yes! All organizations – large or small – use technology and connect to the internet. Unless you have the right security in place, this can leave you vulnerable to cyber-attacks. A well-designed cybersecurity plan will consist of multiple layers of protection, including access limitations, password integrity, email security, secure Wi-Fi, cybersecurity policies, end-user education, data backup and business continuity/disaster recovery.
All of these components come together to protect and defend your systems from cybersecurity incidents, both malicious and accidental.
When an organization is not prepared, when it does not invest in proper cybersecurity planning, it opens itself to risks. The question becomes, What could you lose if a cybersecurity event were to occur? In addition to lost data, you could lose the trust of your partners and users, as well as lost revenue due to downtime and lost productivity.
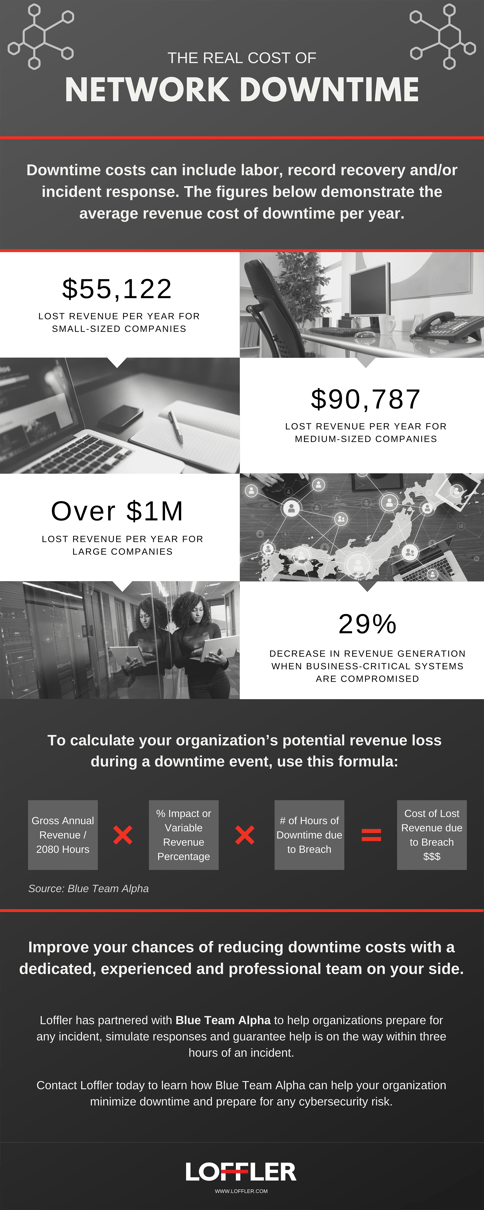
The Real Cost of Network Downtime
One component of a cybersecurity plan is forming an incident response plan. Loffler partners with the organization Blue Team Alpha to help organizations prepare for any incident, simulate responses and guarantee help is on the way within three hours of an incident.
Blue Team Alpha has made it their business to work with organizations to prepare for the worst-case scenario — a data breach, a phishing attack, ransomware— and if that worst-case scenario occurs, they lead the charge in triaging the incident and getting the organization back to business. They estimate an organization can expect a decrease of 29% in revenue generation when business-critical systems are compromised. This can result in tens of thousands of dollars in lost revenue (on the low end).
Questions to Determine Your Downtime Costs
Cyber-attacks have been causing issues for organizations for years, and they're only becoming more common. The longer it takes to restore systems and/or get your data back, the more time and money you lose. For workplaces that are not prepared or able to restore their files from backup, what could an attack cost you? Consider the following questions:
How much does an average employee earn per hour at your workplace?
Take your average employee multiplied by the number of employees in your office. Say you have 30 employees averaging a wage of $30 per hour. That is a minimum of $900 per hour of lost productivity until your data and systems can be recovered and restored. Maybe you can live with an hour ($900 lost) or two of wasted productivity? But what about a whole day ($7,200)? Or a week ($36,000)?
What will you lose in lost revenues or rework?
How much do you average in revenue or billings per day? Or per week? Many ransomware victims lose hours, days or even weeks of production when they do not have, or are not able to recover from, a recent backup. Having to revert to an older version of your data is additional time lost for your organization, while you recreate days or weeks of redundant work effort.
What is the cost of negative publicity and lost confidence of customers?
Organizations are required to report ransomware and phishing compromises to the government and the FBI. Do you want to end up in Sunday’s paper with some “free advertising” for the wrong reasons? Can you afford the risk of customers (and business partners and vendors) losing confidence in working with you?
How much is your business worth to you?
Using the considerations above, you can estimate the cost of downtime for your own organization. But also consider: 60% of small businesses who are victims of a cyber-attack are unable to recover, and close their doors within six months.
Part of our job at Loffler is to keep our clients' names out of the news. We’ve been assisting clients with navigating and recovering from security scams and issues since 2008. To date, we haven’t had a situation where we couldn’t revive the systems. But there have been close calls. And the recovery times and costs have varied widely, depending on:
- The organization's preparedness to defend against such situations
- The maturity level of their backup and recovery technologies and processes
Many small and medium-sized businesses are not prepared to restore their systems from a backup. It’s not really about data backup... it’s about systems recovery.
Want help with your security solutions, practices and processes?

Randy is a CISSP who leads the Cybersecurity and IT Consulting team at Loffler Companies. He is focused on applying his 25+ years of IT experience to help his clients measure, understand and manage information security risk through the vCISO managed consulting program.